Welcome to our
Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.Bypassing Browser Security Policies For Fun And Profit (Blackhat Asia 2016)
published on 2016-03-31 11:49:00 UTC by RafayContent:
Few hours back, i delivered a talk at Blackhat Asia 2016 on "Bypassing Browser Security Policies For Fun And Profit", the talk covered wide variety of topics starting from SOP bypasses, CSP bypass so on and so forth. Due to limited time i was only able to cover few topics, however, you can find rest of the topics in the WhitePaper below. The following was the abstract:
Abstract
'Mobile browsers in comparison to desktop browsers are relatively new and have not gone under same level of scrutiny. Browser vendors have introduced and implemented tons of protection mechanisms against memory corruption exploits, which makes it very difficult to write a reliable exploit that would work under all circumstances. This leaves us with the "other" category of Client Side attacks. In this presentation, we will present our research about bypassing core security policies implemented inside browsers such as the "Same Origin Policy," and "Content Security Policy," etc.
We will present several bypasses that were found in various mobile browsers during our research. In addition, we will also uncover other interesting security flaws found during our research such as Address Bar Spoofing, Content Spoofing, Cross Origin CSS Attacks, Charset Inheritance, CSP Bypass, Mixed Content Bypass, etc., as found in Android Browsers. We will also talk about the testing methodology that we used to uncover several android zero days.
Apart from the theory, our presentation will also disclose a dozen of the most interesting examples of security vulnerabilities and weaknesses highlighted above, which we identified in the most popular Android third-party web browsers, and in Android WebView itself.
We will explain the root cause of the bug and demonstrate their exploitation, show examples of vulnerable code and, where possible, patches that were issued to address these vulnerabilities. Finally, we will demonstrate a sample test suite which can be used to assess basic security properties of any mobile web/browser'
WhitePaper
To download the Whitepaper, please click here.
Slides
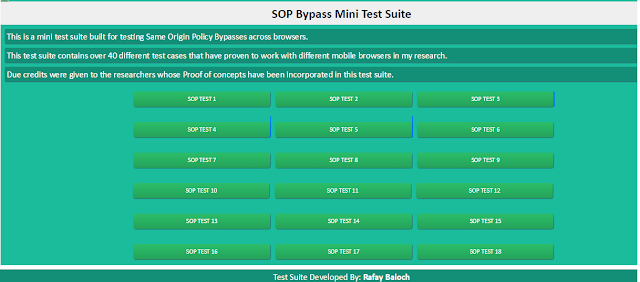
SOP Bypass Mini Test Suite v 1.0 Beta
As promised in my talk, i will make the test suite available on my blog, This test suite contains over 40 different test cases that have proven to work with different mobile browsers in my research or testing Same Origin Policy bypass issues with browsers. Due credits were given to the researchers whose Proof of concepts have been incorporated in this test suite. Please note that, this is just the beta version, the next version would have more test cases and we will try to automate the execution and results of all the test cases.
To download the SOP Bypass Mini Test Suite, please click here.
Shall you have any questions, feel free to ask.
http://www.rafayhackingarticles.net/2016/03/bypassing-browser-security-policies-for-fun-and-profit.html
Published: 2016 03 31 11:49:00
Received: 2022 07 18 17:48:11
Feed: Ethical Hacking - Rafayhackingarticles
Source: Ethical Hacking - Rafayhackingarticles
Category: Cyber Security
Topic: Cyber Security
Views: 16