Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.We Infiltrated a Counterfeit Check Ring! Now What?
published on 2021-06-30 20:34:54 UTC by BrianKrebsContent:
Imagine waking up each morning knowing the identities of thousands of people who are about to be mugged for thousands of dollars each. You know exactly when and where each of those muggings will take place, and you’ve shared this information in advance with the authorities each day for a year with no outward indication that they are doing anything about it. How frustrated would you be?
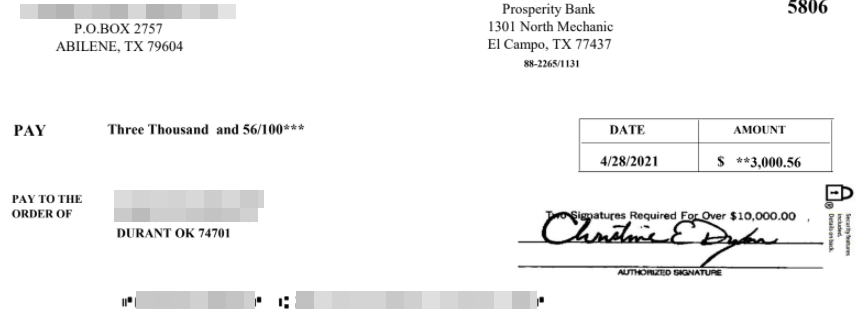
A counterfeit check image [redacted] that was intended for a person helping this fraud gang print and mail phony checks tied to a raft of email-based scams. One fraud-fighting group is intercepting hundreds to thousands of these per day.
Such is the curse of the fraud fighter known online by the handles “Brianna Ware” and “B. Ware” for short, a longtime member of a global group of volunteers who’ve infiltrated a cybercrime gang that disseminates counterfeit checks tied to a dizzying number of online scams.
For the past year, B. Ware has maintained contact with an insider from the criminal group that’s been sending daily lists of would-be victims who are to receive counterfeit checks printed using the real bank account information of legitimate companies.
“Some days we’re seeing thousands of counterfeit checks going out,” B. Ware said.
The scams used in connection with the fraudulent checks vary widely, from fake employment and “mystery shopper” schemes to those involving people who have been told they can get paid to cover their cars in advertisements (a.k.a. the “car wrap” scam).
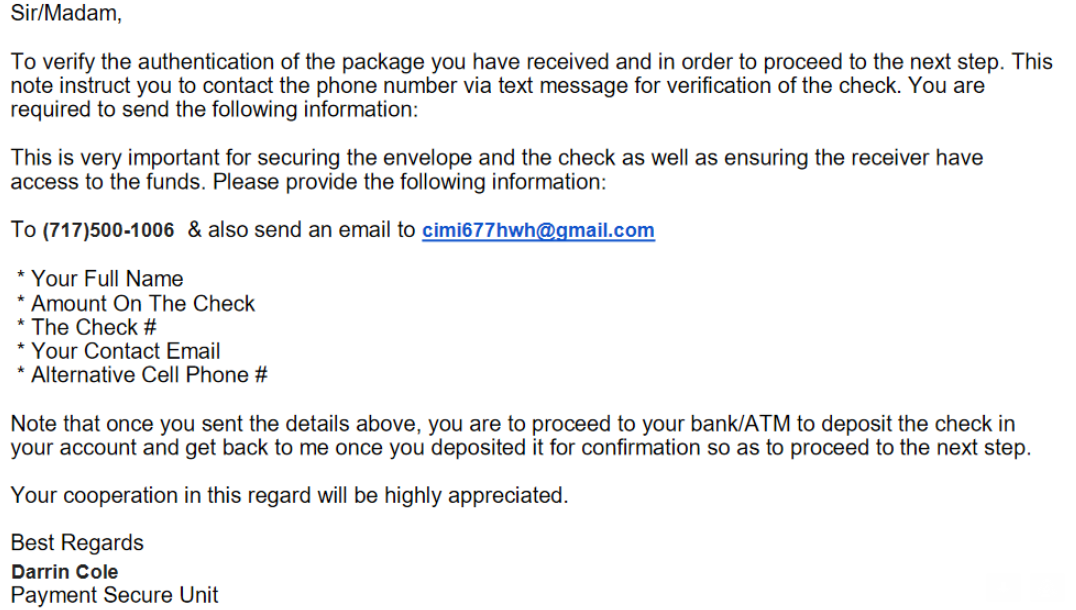
A form letter mailed out with a counterfeit check urges the recipient to text a phone number after the check has been deposited.
Most of the counterfeit checks being disseminated by this fraud group are in amounts ranging from $2,500 to $5,000. The crimes that the checks enable are known variously as “advanced fee” scams, in that they involve tricking people into making payments in anticipation of receiving something of greater value in return.
But in each scheme the goal is the same: Convince the recipient to deposit the check and then wire a portion of the amount somewhere else. A few days after the check is deposited, it gets invariably canceled by the organization whose bank account information was on the check. And then person who deposited the phony check is on the hook for the entire amount.
“Like the car wrap scam, where they send you a check for $5,000, and you agree to keep $1,000 for your first payment and send the rest back to them in exchange for the car wrap materials,” B. Ware said. “Usually the check includes a letter that says they want you to text a specific phone number to let them know you received the check. When you do that, they’ll start sending you instructions on how and where to send the money.”
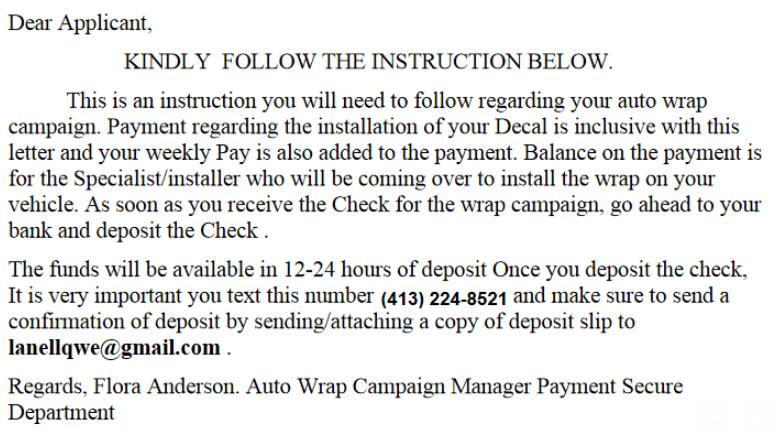
A typical confirmation letter that accompanies a counterfeit check for a car wrap scam.
Traditionally, these groups have asked recipients to transit money via wire transfer. But these days, B. Ware said, the same crooks are now asking people to forward the money via mobile applications like CashApp and Venmo.
B. Ware and other volunteer fraud fighters believe the fake checks gang is using people looped into phony employment schemes and wooed through online romance scams to print the counterfeit checks, and that other recruits are responsible for mailing them out each day.
“More often than not, the scammers creating the shipping labels will provide those to an unwitting accomplice, or the accomplice is told to log in to an account and print the labels,” B. Ware explained.
Often the counterfeit checks and labels forwarded by B. Ware’s informant come with notes attached indicating the type of scam with which they are associated.
“Sometimes they’re mystery shopper scams, and other times it’s overpayment for an item sold on Craigslist,” B. Ware said. “We don’t know how the scammers are getting the account and routing numbers for these checks, but they are drawn on real companies and always scan fine through a bank’s systems initially. The recipients can deposit them at any bank, but we try to get the checks to the banks when we can so they have a heads up.”
SHRINKING FROM THE FIREHOSE?
Roughly a year ago, B. Ware’s group started sharing its intelligence with fraud investigators at FedEx and the U.S. Postal Service — the primary delivery mechanisms for these counterfeit checks.
 Both the USPS and FedEx have an interest in investigating because the fraudsters in this case are using stolen shipping labels paid for by companies who have no idea their FedEx or USPS accounts are being used for such purposes.
Both the USPS and FedEx have an interest in investigating because the fraudsters in this case are using stolen shipping labels paid for by companies who have no idea their FedEx or USPS accounts are being used for such purposes.
“In most cases, the name of the sender will be completely unrelated to what’s being sent,” B. Ware said. “For example, you’ll see a label for a letter to go out with a counterfeit check for a car wrap scam, and the sender on the shipping label will be something like XYZ Biological Resources.”
But B. Ware says a year later, there is little sign that anyone is interested in acting on the shared intelligence.
“It’s so much information that they really don’t want it anymore and they’re not doing anything about it,” B. Ware said of FedEx and the USPS. “It’s almost like they’re turning a blind eye. There are so many of these checks going out each day that instead of trying to drink from the firehouse, they’re just turning their heads.”
FedEx did not respond to requests for comment. The U.S. Postal Inspection Service responded with a statement saying it “does not comment publicly on its investigative procedures and operational protocols.”
ANY METHOD THAT WORKS
Ronnie Tokazowski is a threat researcher at Agari, a security firm that has closely tracked many of the groups behind these advanced fee schemes [KrebsOnSecurity interviewed Tokazowski in 2018 after he received a security industry award for his work in this area].
Tokazowski said it’s likely the group B. Ware has infiltrated is involved in a myriad other email fraud schemes, including so-called “business email compromise” (BEC) or “CEO scams,” in which the fraudsters impersonate executives at a company in the hopes of convincing someone at the firm to wire money for payment of a non-existent invoice. According to the FBI, BEC scams netted thieves nearly $2 billion in 2020 — far more than any other type of cybercrime.
In a report released in 2019 (PDF), Agari profiled a group it dubbed “Scattered Canary” that is operating principally out of West Africa and dabbles in a dizzying array of schemes, including BEC and romance scams, FEMA and SBA loans, unemployment insurance fraud, counterfeit checks and of course money laundering.
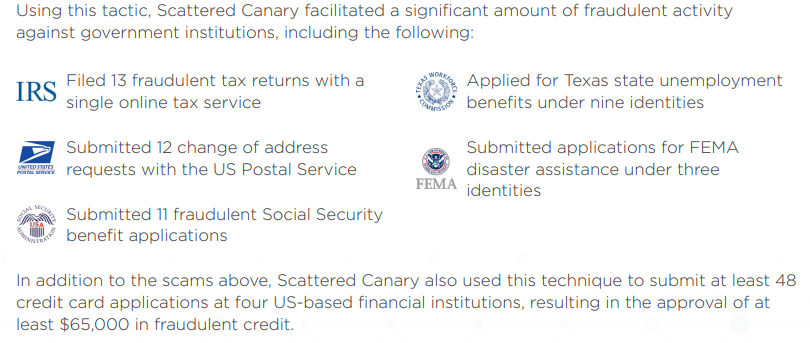
Image: Agari.
Tokazowski said he doesn’t know if the group B. Ware is watching has any affiliation with Scattered Canary. But he said his experience with Scattered Canary shows these groups tend to make money via any and all methods that reliably produce results.
“One of the things that came out of the Scattered Canary report was that the actors we saw doing BEC scams were the same actors doing the car wrap and various Craigslist scams involving fake checks,” he said. “The people doing this type of crime will have tutorials on how to run the scam, how to wire money out for unemployment fraud, how to target people on Craigslist, and so on. It’s very different from the way a Russian hacking group might go after one industry vertical or piece of software or focus on one or two types of fraud. They will follow any method they can that works.”
Tokazowski said he’s taken his share of flack from people on social media who say his focus on West African nations as the primary source of these advanced fee and BEC scams is somehow racist [KrebsOnSecurity experienced a similar response to the 2013 stories, Spy Service Exposes Nigerian ‘Yahoo Boys’, and ‘Yahoo Boys’ Have 419 Facebook Friends].
But Tokazowski maintains he has been one of the more vocal proponents of the idea that trying to fight these problems by arresting those involved is something of a Sisyphean task, and that it makes way more sense to focus on changing the economic realities in places like Nigeria, which has been a hotbed of advanced fee activity for decades.
Nigeria has the world’s second-highest unemployment rate — rising from 27.1 percent in 2019 to 33 percent in 2020, according to the National Bureau of Statistics. The nation also is among the world’s most corrupt, according to 2020 findings from Transparency International.
“Education is definitely one piece, as raising awareness is hands down the best way to get ahead of this,” Tokazowski said. “But we also need to think about ways to create more business opportunities there so that people who are doing this to put food on the table have more legitimate opportunities. Unfortunately, thanks to the level of corruption of government officials, there are a lot of cultural reasons that fighting this type of crime at the source is going to be difficult.”
https://krebsonsecurity.com/2021/06/we-infiltrated-a-counterfeit-check-ring-now-what/
Published: 2021 06 30 20:34:54
Received: 2021 06 30 21:06:16
Feed: Krebs on Security
Source: Krebs on Security
Category: Cyber Security
Topic: Cyber Security
Views: 27
