Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.Hacked Ring Cams Used to Record Swatting Victims
published on 2022-12-20 01:24:10 UTC by BrianKrebsContent:

Photo: BrandonKleinPhoto / Shutterstock.com
Two U.S. men have been charged with hacking into the Ring home security cameras of a dozen random people and then “swatting” them — falsely reporting a violent incident at the target’s address to trick local police into responding with force. Prosecutors say the duo used the compromised Ring devices to stream live video footage on social media of police raiding their targets’ homes, and to taunt authorities when they arrived.
Prosecutors in Los Angeles allege 20-year-old James Thomas Andrew McCarty, a.k.a. “Aspertaine,” of Charlotte, N.C., and Kya Christian Nelson, a.k.a. “ChumLul,” 22, of Racine, Wisc., conspired to hack into Yahoo email accounts belonging to victims in the United States. From there, the two allegedly would check how many of those Yahoo accounts were associated with Ring accounts, and then target people who used the same password for both accounts.
An indictment unsealed this week says that in the span of just one week in November 2020, McCarty and Nelson identified and swatted at least a dozen different victims across the country.
“The defendants then allegedly accessed without authorization the victims’ Ring devices and transmitted the audio and video from those devices on social media during the police response,” reads a statement from Martin Estrada, the U.S. Attorney for the Central District of California. “They also allegedly verbally taunted responding police officers and victims through the Ring devices during several of the incidents.”

James Thomas Andrew McCarty.
The indictment charges that McCarty continued his swatting spree in 2021 from his hometown in Kayenta, Ariz., where he called in bomb threats or phony hostage situations on more than two dozen occasions.
The Telegram and Discord aliases allegedly used by McCarty — “Aspertaine” and “Couch,” among others — correspond to an identity that was active in certain channels dedicated to SIM-swapping, a crime that involves stealing wireless phone numbers and hijacking the online financial and social media accounts tied to those numbers.
Aspertaine bragged on Discord that he’d amassed more than $330,000 in virtual currency. On Telegram, the Aspertaine/Couch alias frequented several popular SIM-swapping channels, where they initially were active as a “holder” — a low-level but key SIM-swapping group member who agrees to hold stolen cryptocurrency after an account takeover is completed. Aspertaine later claimed more direct involvement in individual SIM-swapping attacks.
In September, KrebsOnSecurity broke the news about a wide-ranging federal investigation into “violence-as-a-service” offerings on Telegram and other social media networks, wherein people can settle scores by hiring total strangers to carry out physical attacks such as brickings, shootings, and firebombings at a target’s address.
The story observed that SIM swappers were especially enamored of these “IRL” or “In Real Life” violence services, which they frequently used to target one another in response to disagreements over how stolen money should be divided amongst themselves. And a number of Aspertaine’s peers on these SIM-swapping channels claimed they’d been ripped off after Aspertaine took more than a fair share from them.
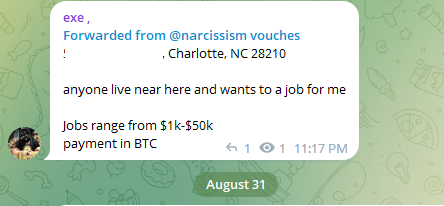
In August, a member of a popular SIM-swapping group on Telegram who was slighted by Aspertaine put out the word that he was looking for some physical violence to be visited on McCarty’s address in North Carolina. “Anyone live near here and wants to [do] a job for me,” the job ad with McCarty’s home address read. “Jobs range from $1k-$50k. Payment in BTC [bitcoin].” It’s unclear if anyone responded to that job offer.
KrebsOnSecurity recently published The Wages of Password ReUse: Your Money or Your Life, which noted that when normal computer users fall into the nasty habit of recycling passwords, the result is most often some type of financial loss. Whereas, when cybercriminals reuse passwords, it often costs them their freedom.
But perhaps that story should be updated, because it’s now clear that password reuse can also put you in mortal danger. Swatting attacks are dangerous, expensive hoaxes that sometimes end in tragedy.
In June 2021, an 18-year-old serial swatter from Tennessee was sentenced to five years in prison for his role in a fraudulent swatting attack that led to the death of a 60-year-old man.
In 2019, prosecutors handed down a 20-year sentence to Tyler Barriss, a then 26-year-old serial swatter from California who admitted making a phony emergency call to police in late 2017 that led to the shooting death of an innocent Kansas man.
McCarty was arrested last week, and charged with conspiracy to intentionally access computers without authorization. Prosecutors said Nelson is currently incarcerated in Kentucky in connection with unrelated investigation.
If convicted on the conspiracy charge, both defendants would face a statutory maximum penalty of five years in federal prison. The charge of intentionally accessing without authorization a computer carries a maximum possible sentence of five years. A conviction on the additional charge against Nelson — aggravated identity theft — carries a mandatory two-year consecutive sentence.
https://krebsonsecurity.com/2022/12/hacked-ring-cams-used-to-record-swatting-victims/
Published: 2022 12 20 01:24:10
Received: 2022 12 20 16:01:01
Feed: Krebs on Security
Source: Krebs on Security
Category: Cyber Security
Topic: Cyber Security
Views: 13
