Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.Data Breach Misattribution, Acxiom & Live Ramp
published on 2022-11-22 20:06:51 UTC by Troy HuntContent:
If you find your name and home address posted online, how do you know where it came from? Let's assume there's no further context given, it's just your legitimate personal data and it also includes your phone number, email address... and over 400 other fields of data. Where on earth did it come from? Now, imagine it's not just your record, but it's 246 million records. Welcome to my world.
This is a story about a massive corpus of data circulating widely within the hacking community and misattributed to a legitimate organisation. That organisation is Acxiom, and their business hinges on providing their customers with data on their customers. By the very nature of their business, they process large volumes of data that includes a broad set of personal attributes. By pure coincidence, there is nominal commonality between Acxiom’s records and the ones in the 246M corpus I mentioned earlier. But I'm jumping ahead to the conclusion, let's go back to the beginning:
Disclosure and Attribution Debunking
In June last year, I received an email from someone I trust who had sent me data for Have I Been Pwned (HIBP) in the past:
Have you seen Axciom [sic] data? It was just sent to us. Seems to being traded/sold on some forums. Have you received it yet? If not i can upload it for you. It's quite large tho, ~250M Records.
A corpus of data that size is particularly interesting as it impacts such a huge number of people. So, I reviewed the data and concluded... pretty much nothing. Looks legit, smells legit but there was absolutely nothing beyond the word of one person to tie it to Acxiom (and who knows who they got that word from). Burdened by other more immediately actionable data breaches, I filed it away until recently when that name popped up again, this time on a popular hacking forum:
It was referred to as "LiveRamp (Formerly Acxiom)" and before I go any further, let's just clarify the problem with that while you're looking at the image above: LiveRamp was previously a subsidiary of Acxiom, but that hasn't been the case since they separated businesses in 2018 so whoever put this together is referring back to a very old state of play. Regardless, those downloading it from the forum were clearly very excited about it. Seeing this for the second time and spreading far more broadly, I decided to reach out to the (alleged) source and ask Acxiom what was going on.
I dread this process - contacting an organisation about a breach - because I usually get either no response whatsoever or a standoffish one. Rarely do I find a receptive organisation willing to fully investigate an alleged incident, but that's exactly what I found on this occasion. Much of the reason why I wanted to write this post is because whilst I hate breached organisations not properly investigating an incident, I also hate seeing misattribution of a breach to an innocent party. That's a particularly sore point for me right now because of this incident just last week:
This is the dumbest infosec story I’ve read in… forever? It is so profoundly incorrect, poorly researched, never verified, rambling and indistinguishable from parody that I literally went looking for the parody reference. I think he’s actually serious! https://t.co/oLyIHxb8D3
— Troy Hunt (@troyhunt) November 15, 2022
I've had various public users of HIBP, commercial users and even governments reach out to ask what's going on because they were concerned about their data. Whilst this incident won't do HIBP any actual harm (and frankly, I'm stunned anyone took that story seriously), I can very easily see how misattribution can be damaging to an organisation, indeed that's a key reason why I invest so much effort into properly investigating these claims before putting anything into HIBP. But that ridiculous example is nothing compared to the amount of traction some misattributions get. Remember how just recently a couple of billion TikTok accounts had been "breached"? This made massive news headlines until...
The thread on the hacking forum with the samples of alleged TikTok data has been deleted and the user banned for “lying about data breaches” https://t.co/9ZKkKvu8JT
— Troy Hunt (@troyhunt) September 5, 2022
"Lying about data breaches". Ugh, criminals are so untrustworthy! This happens all the time and when I'm not sure of the origin of a substantial breach, I often write a blog post like this and on many occasions, the masses help establish the origin. So, here goes:
The Data
Let's jump into the data, starting with 2 of the most obvious things I look for in any new data breach:
- The total number of unique email addresses is 51,730,831 (many records don't have this field populated)
- The most recent data I can find is from mid-2020 (which also speaks to the inaccuracy of the LiveRamp association)
As to the aforementioned attributes, they total 410 different columns:
| AddressID | |
| IndividualId | |
| personfirstname | |
| personmiddleinitial | |
| personlastname | |
| PersonSurnameSuffix | |
| persontitleofrespect | |
| housenumber | |
| predirection | |
| streetname | |
| streetsuffix | |
| postdirection | |
| unitdesignator | |
| unitdesignatornumber | |
| primaryaddress | |
| secondaryaddress | |
| state | |
| ZipCode | |
| Zip_4 | |
| del_point_check_digit | |
| msa | |
| countycode | |
| countyname | |
| citynameabbr | |
| cityname | |
| carrier_route | |
| censustract | |
| censusblock | |
| latitude | |
| longitude | |
| timezone | |
| Xaxis | |
| Yaxis | |
| Zaxis | |
| dpv_code | |
| NumberOfSources | |
| dwellingtype | |
| secondaryaddresspresent | |
| livingunitid | |
| RDID | |
| Phone | |
| estimatedincomecode | |
| homeownerprobabilitymodel | |
| lengthofresidence | |
| lengthofresidencecode | |
| numberofpersonsinlivingunit | |
| presenceofchildren | |
| NumberOfChildren | |
| ChildrenAge00_02 | |
| ChildrenAge00_02Male | |
| ChildrenAge00_02Female | |
| ChildrenAge00_02Unknown | |
| ChildrenAge03_05 | |
| ChildrenAge03_05Male | |
| ChildrenAge03_05Female | |
| ChildrenAge03_05Unknown | |
| ChildrenAge06_10 | |
| ChildrenAge06_10Male | |
| ChildrenAge06_10Female | |
| ChildrenAge06_10Unknown | |
| ChildrenAge11_15 | |
| ChildrenAge11_15Male | |
| ChildrenAge11_15Female | |
| ChildrenAge11_15Unknown | |
| ChildrenAge16_17 | |
| ChildrenAge16_17Male | |
| ChildrenAge16_17Female | |
| ChildrenAge16_17Unknown | |
| persongender | |
| persondateofbirthyear | |
| persondateofbirthmonth | |
| persondateofbirthday | |
| personexactage | |
| personagecode | |
| Males_18_24 | |
| Females_18_24 | |
| Unknowngender_18_24 | |
| Males_25_34 | |
| Females_25_34 | |
| Unknowngender_25_34 | |
| Males_35_44 | |
| Females_35_44 | |
| Unknowngender_35_44 | |
| Males_45_54 | |
| Females_45_54 | |
| Unknowngender_45_54 | |
| Males_55_64 | |
| Females_55_64 | |
| Unknowngender_55_64 | |
| Males_65_74 | |
| Females_65_74 | |
| Unknowngender_65_74 | |
| Males_75_Plus | |
| Females_75_Plus | |
| Unknowngender_75_Plus | |
| personmaritalstatus | |
| InferredAge | |
| occupationgroup | |
| personoccupation | |
| ethniccode | |
| languagecode | |
| ethnicgroup | |
| religioncode | |
| hispaniccountrycode | |
| personeducation | |
| businessowner | |
| EthnicConfidenceCode | |
| InferredHouseholdRank | |
| NumberOfAdults | |
| GenerationsInHousehold | |
| PresenceOfCreditCard | |
| presenceofgoldorplatinumcreditcard | |
| PresenceOfPremiumCreditCard | |
| PresenceOfUpscaleRetailCard | |
| PresenceOfBankCard | |
| GasDeptRetailCardHolder | |
| americanexpresscard | |
| CreditRating | |
| investment | |
| investmentstocksecurities | |
| Networth | |
| NumberOfLinesOfCredit | |
| Credit_RangeOfNewCredit | |
| AmericanExpressGoldPremium | |
| DiscoverGoldPremium | |
| DiscoverRegular | |
| GasolineOrRetailCardGoldPremium | |
| GASOLINE OR RETAIL CARD REGULAR | |
| MastercardGoldPremium | |
| MastercardRegular | |
| VisaGoldPremium | |
| VisaRegular | |
| CREDIT CARD INDICATOR | |
| BANK CARD HOLDER | |
| GAS/DEPARTMENT/RETAIL CARD HOLDER | |
| TravelAndEntertainmentCardHolder | |
| CreditCardholderUnknownType | |
| PREMIUM CARD HOLDER | |
| UPSCALE (DEPARTMENT STORE) CARD HOLDER | |
| CreditCardUser | |
| CreditCardNewIssue | |
| BANK CARD - PRESENCE IN HOUSEHOLD | |
| Investing_Active | |
| InvestmentsPersonal | |
| InvestmentsRealEstate | |
| InvestingFinanceGrouping | |
| InvestmentsForeign | |
| InvestmentEstimatedResidentialPropertiesOwned | |
| AssimilationCodes | |
| valuehunter | |
| opportunityseekers | |
| newsandfinancial | |
| automotivebuff | |
| bookreader | |
| MembershipClub | |
| computerowner | |
| cookingenthusiast | |
| do_it_yourselfers | |
| exerciseenthusiast | |
| Gardener | |
| golfenthusiasts | |
| homedecoratingenthusiast | |
| outdoorenthusiast | |
| outdoorsportslover | |
| photography | |
| traveler | |
| pets | |
| cats | |
| dogs | |
| mailresponder | |
| RespondedtoCatalog | |
| sweepstakes | |
| religiousmagazine | |
| malemerchbuyer | |
| femalemerchbuyer | |
| crafts_hobbmerchbuyer | |
| gardening_farmingbuyer | |
| bookbuyer | |
| collect_specialfoodsbuyer | |
| religiouscontributor | |
| politicalcontributor | |
| health_institutioncontributor | |
| charitable | |
| generalcontributor | |
| donatestoenvironmentalcauses | |
| donatesbymail | |
| veteraninhousehold | |
| HeavyBusinessTravelers | |
| hightechleader | |
| Smoker | |
| MailOrderBuyer | |
| OnlinePurchasingIndicator | |
| ApparelWomens | |
| ApparelWomensPetite | |
| ApparelWomensPlusSizes | |
| YoungWomensApparel | |
| ApparelMens | |
| ApparelMensBigAndTall | |
| YoungMensApparel | |
| ApparelChildrens | |
| HealthAndBeauty | |
| BeautyCosmetics | |
| Jewelry | |
| Luggage | |
| COMMUNITY INVOLVEMENT - CAUSES SUPPORTED FINANCIALLY | |
| AnimalWelfareCharitableDonation | |
| ArtsOrCulturalCharitableDonation | |
| ChildrensCharitableDonation | |
| ENVIRONMENT OR WILDLIFE CHARITABLE DONATION | |
| EnvironmentalIssuesCharitableDonation | |
| InternationalAidCharitableDonation | |
| PoliticalCharitableDonation | |
| PoliticalConservativeCharitableDonation | |
| PoliticalLiberalCharitableDonation | |
| VeteransCharitableDonation | |
| CharitableDonations_Other | |
| CommunityCharities | |
| Parenting | |
| SingleParent | |
| ChildrensApparelInfantsAndToddlers | |
| ChildrensLearningAndActivityToys | |
| ChildrensProductsGeneralBabyCare | |
| ChildrensProductsGeneralBackToSchool | |
| ChildrensProductsGeneral | |
| YoungAdultInHousehold | |
| SeniorAdultInHousehold | |
| ChildrensInterests | |
| Grandchildren | |
| ChristianFamilies | |
| Equestrian | |
| OtherPetOwner | |
| CareerImprovement | |
| WorkingWoman | |
| AfricanAmericanProfessionals | |
| SohoIndicator | |
| Career | |
| BooksAndMagazinesMagazines | |
| BooksAndMusicBooks | |
| BooksAndMusicBooksAudio | |
| ReadingGeneral | |
| READING - RELIGIOUS / INSPIRATIONAL | |
| ReadingScienceFiction | |
| ReadingMagazines | |
| ReadingAudioBooks | |
| ReadingGrouping | |
| HistoryMilitary | |
| CurrentAffairsPolitics | |
| ReligiousInspirational | |
| ScienceSpace | |
| Magazines | |
| EducationOnline | |
| Gaming | |
| ComputingHomeOfficeGeneral | |
| DVDsVideos | |
| ElectronicsandComputingTVVideoMovieWatcher | |
| ElectronicsComputingAndHomeOffice | |
| HighEndAppliances | |
| IntendToPurchaseHDTVSatelliteDish | |
| MusicHomeStereo | |
| MusicPlayer | |
| MusicCollector | |
| MusicAvidListener | |
| MovieCollector | |
| TVCable | |
| GamesVideoGames | |
| TVSatelliteDish | |
| COMPUTERS | |
| GamesComputerGames | |
| ConsumerElectronics | |
| MovieMusicGrouping | |
| ElectronicsComputersGrouping | |
| Telecommunications | |
| ArtsAndAntiquesAntiques | |
| ArtsAndAntiquesArt | |
| TheaterPerformingArts | |
| Arts | |
| Musicalinstruments | |
| CollectiblesGeneral | |
| CollectiblesStamps | |
| CollectiblesCoins | |
| CollectiblesArts | |
| CollectiblesAntiques | |
| CollectorAvid | |
| CollectiblesandAntiquesGrouping | |
| CollectiblesSportsMemorabilia | |
| MilitaryMemorabiliaWeaponry | |
| LifestylesInterestsandPassionsCollectibles | |
| Autowork | |
| SewingKnittingNeedlework | |
| Woodworking | |
| Aviation | |
| HousePlants | |
| Crafts | |
| HomeandGarden | |
| GARDENING | |
| GARDENING2 | |
| HomeImprovementGrouping | |
| PhotographyAndVideoEquipment | |
| HomeFurnishingsDecorating | |
| HomeImprovement | |
| IntendtoPurchaseHomeImprovement | |
| FoodWines | |
| CookingGeneral | |
| COOKING - GOURMET | |
| FoodsNatural | |
| CookingFoodGrouping | |
| GamesBoardGamesPuzzles | |
| GamingCasino | |
| TravelGrouping | |
| TRAVEL | |
| TravelDomestic | |
| TravelInternational | |
| TravelCruiseVacations | |
| HomeLiving | |
| DIYLiving | |
| SportyLiving | |
| UpscaleLiving | |
| CulturalArtisticLiving | |
| Highbrow | |
| HIGH-TECH LIVING | |
| CommonLiving | |
| ProfessionalLiving | |
| BroaderLiving | |
| ExerciseHealthGrouping | |
| ExerciseRunningJogging | |
| ExerciseWalking | |
| ExerciseAerobic | |
| SpectatorSportsAutoMotorcycleRacing | |
| SpectatorSportsTVSports | |
| SpectatorSportsFootball | |
| SpectatorSportsBaseball | |
| SpectatorSportsBasketball | |
| SpectatorSportsHockey | |
| SpectatorSportsSoccer | |
| Tennis | |
| Snowskiing | |
| Motorcycling | |
| Nascar | |
| BoatingSailing | |
| ScubaDiving | |
| SportsandLeisure | |
| Hunting | |
| Fishing | |
| CampingHiking | |
| HuntingShooting | |
| SportsGrouping | |
| OutdoorsGrouping | |
| HealthMedical | |
| DietingWeightLoss | |
| SelfImprovement | |
| AutomotiveAutoPartsAndAccessories | |
| RDI | |
| homeswimmingpoolindicator | |
| airconditioning | |
| homeheatindicator | |
| homepurchaseprice | |
| homepurchasepricecode | |
| homepurchasedateyear | |
| homepurchasedatemonth | |
| homepurchasedateday | |
| homeyearbuilt | |
| estimatedcurrenthomevaluecode | |
| mortgageamountinthousands | |
| mortgageamountinthousandscode | |
| mortgagelendername | |
| mortgagelendernameavailable | |
| mortgagerate | |
| mortgageratetype | |
| mortgageloantype | |
| transactiontype | |
| deeddateofrefinanceyear | |
| deeddateofrefinancemonth | |
| deeddateofrefinanceday | |
| refinanceamountinthousands | |
| refinanceamountinthousandscode | |
| refinancelendername | |
| refinancelendernameavailable | |
| refinanceratetype | |
| refinanceloantype | |
| CensusMedianHomeValue | |
| CensusMedianHouseholdIncome | |
| CRA_IncomeClassificationCode | |
| MostRecentMortgageAmount2nd | |
| Purchase2ndMortgageAmount | |
| MostRecentMortgageDate2nd | |
| PurchaseMortgageDate | |
| MostRecentMortgage2ndLoanTypeCode | |
| Purchase2ndMortgageLoanTypeCode | |
| MostRecentLenderCode | |
| MostRecent2ndLenderCode | |
| PurchaseLenderCode | |
| MostRecentLenderName2nd | |
| PURCHASE LENDER NAME | |
| MostRecentMortgage2ndInterestRateType | |
| Purchase2ndMortgageInterestRateType | |
| MostRecentMortgageInterestRate | |
| MostRecentMortgage2ndInterestRate | |
| Purchase2ndMortgageInterestRate | |
| Sewer | |
| Water | |
| LoanToValue | |
| PassProspectorValueHomeValueMortgageFile | |
| EMAILFLAG | |
| NCOA_Effective_date | |
| DONOTCALL | |
| NAME | |
| URL | |
| IP | |
| DATE |
To my eye, this data is very generic and looks like a superset of information that may be collected across a large number of people. For example, the sort of data requested when filling out dodgy online competitions. However, unlike many large corpuses of aggregated data I've seen in the past, this one is... neat. For example, here's a little sample of the first 5 columns (redaction of some chars with a dash), note how the names are all uniformly presented:
120321486,4,BE-----,B,TAYLOR
120321487,2,JOY,M,----EY
120321466,1,DOYLE,E,------HAM
120321486,3,L----,,TAYLOR
120321486,2,R---,M,TAYLORSure, this is just uppercasing characters but over and over again, I found data that was just too neat. The addresses. The phone numbers. Everything about it was far to curated to simply be text entered by humans. My suspicion is that it's likely a result of either a very refined collection process or in the case of addresses, matched using a service to resolve the human-entered address to a normalised form stored centrally.
Perhaps what I was most interested in though was the URL column as that seems to give some indication of where the data might have come from. I queried out the top 100 most common ones and took a look:
| DIRECTEDUCATIONCENTER.COM 661118 | |
| originalcruisegiveaway.com 539101 | |
| free-ukstuff.com 383523 | |
| findyourdegreenow.com 375841 | |
| getmysolarpower.com 343505 | |
| disabilitybenefitscenter.org 319822 | |
| PDILOANS.COM 243174 | |
| TAGGED.COM 237474 | |
| GadgetCenter.us.com 227834 | |
| youreducationsearch.com 226130 | |
| COUPONDISCOUNTCLUB.COM 226012 | |
| collegedegreesforme.com 214123 | |
| bestnetfreebies.com 209096 | |
| popularliving.com 203610 | |
| ONLINEDEGREERADAR.COM 201212 | |
| 123freetravel.com 195579 | |
| persopo.com/assembling-report/ready 184637 | |
| insuranceforallonline.com 174576 | |
| homepowerprofits.com 167702 | |
| dermologykit.com/ 166653 | |
| getcashhelp.com 163817 | |
| EMPLOYMENTSEARCHUSA.COM 159505 | |
| lowcostinsuranceguide.com 158838 | |
| coolsavings.com 158597 | |
| FILEFORGRANTS.COM 156478 | |
| INSUREDATLAST.COM 151221 | |
| progressivebusinesssystems.com 149282 | |
| SAVEANDSMILE.COM 146055 | |
| ProjectPayday.com 145770 | |
| getlife-insurance.com 143934 | |
| PAYDAYLOANEVERYDAY.COM 142469 | |
| ALLSTATESDEBT.COM 140008 | |
| SNAPPYCARINSURANCE.COM 138858 | |
| CONSUMERREWARDS.US.COM 135912 | |
| progressivejoblistings.com 135194 | |
| quickquid.co.uk 133676 | |
| yourfreequotes.com 131949 | |
| publicsurveypanel.com 130969 | |
| bigvacationgiveaway.com 130687 | |
| selfwealthsystem.com 129609 | |
| IMMEDIATEPAYCHECK.COM 128145 | |
| alwayscashloans.com 126180 | |
| cosmeticsplace.net 126099 | |
| individualhealthquotes.com 124813 | |
| emortgagefinders.com 124173 | |
| CAREERANDEDUCATIONCENTER.COM 123968 | |
| AttentionShoppers.us.com 123087 | |
| jobs-resource.com 122473 | |
| insureqlick.com 120876 | |
| therefiadvisor.com 120431 | |
| SAMPLESANDREBATES.COM 120281 | |
| HBWM.COM 119916 | |
| buy.com 118839 | |
| elitecashwire.com 118086 | |
| planetminecraft.com 117109 | |
| NEWSTARTEDUCATION.COM 112161 | |
| creditreport.com 111162 | |
| instantadvancepay.com 110439 | |
| I-DEALREWARDS.COM 110053 | |
| cashexpert.com 109992 | |
| NEWBEGINNINGCREDIT.COM 109553 | |
| CREDITREPAIR.COM 107834 | |
| cashlendernetwork.com 107559 | |
| homepayopportunity.com 107303 | |
| courseadvisor.com 106588 | |
| HIGHEREDUCATIONSEEKER.COM 106290 | |
| dailyhealthcentral.com 104354 | |
| GETYOURCHECKTODAY.COM 104026 | |
| CARDAPPROVALUSA.COM 103484 | |
| findaquote.net 102488 | |
| extraincomehelps.com 102264 | |
| HOMEOPPORTUNITYCENTRAL.COM 101655 | |
| icoulduseajob.com 101643 | |
| ifortunebuilder.com 101274 | |
| BOXLOTTO.COM 101155 | |
| PAYCHECKADVANCETODAY.COM 101094 | |
| healthplanwiz.com 100523 | |
| grandsavingscenter.com 99913 | |
| elitecareerseekers.com 99436 | |
| discountclubfinder.com 98843 | |
| nationalcreditreport.com 98489 | |
| cashadvance.com 98407 | |
| freecreditclick.com 98343 | |
| 37clicks.com 97157 | |
| myshopdiscounts.com 96817 | |
| consumergiftcenter.us.com 96489 | |
| cashgalore.net 96154 | |
| disabilityapprovalguide.com 94873 | |
| couponclipclub.com 94129 | |
| paydaycashnet.com 94000 | |
| careersmaster.com 93905 | |
| targetedcareer.com 93613 | |
| greenpayday.com 93358 | |
| timelypayday.com 93158 | |
| nationalpayday.com 92856 | |
| creditfixerscentral.com 92127 | |
| collegefindercenter.com 91664 | |
| PINNACLEINSURANCESELECT.COM 90965 | |
| overnightpaycheck.com 90900 | |
| betterinsurancechoice.com 90849 |
Eyeballing them, I couldn't help feel that my earlier hunch was on the money - "dodgy online competitions". Not just competitions but a general theme of getting stuff for cheap or more specifically, services that look like they've been built to entice people to part with their personal data.
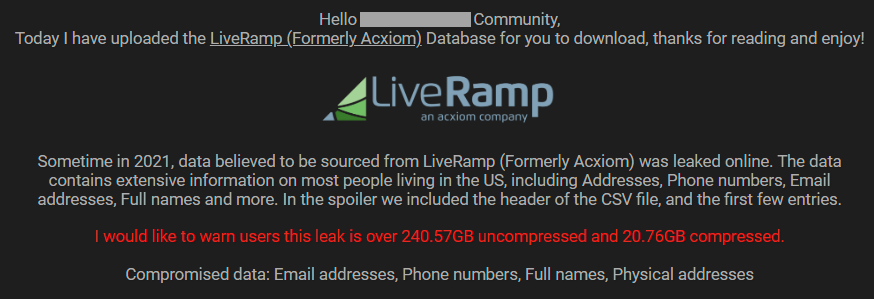
Take the first one, for example, DIRECTEDUCATIONCENTER.COM. That's a dead domain as of now but check out what it looked line in March last year:
"I may be contacted by trusted partners and others". What's "others"? Untrusted partners? 🤷♂️
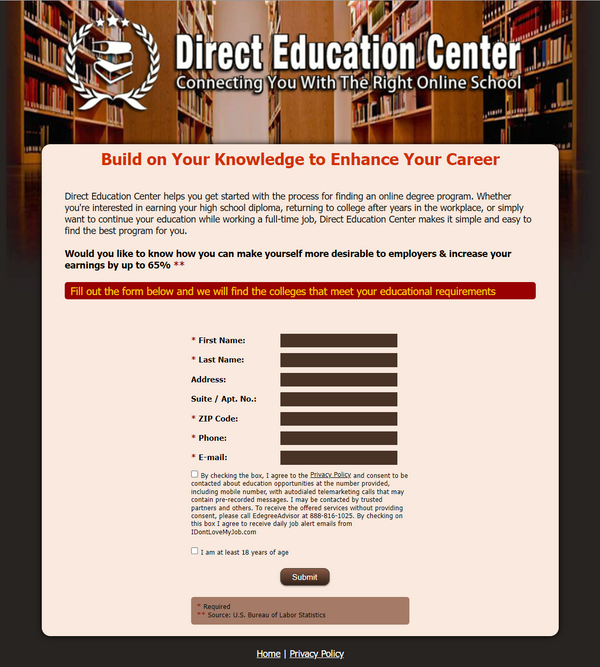
Let's try the next one being originalcruisegiveaway.com and again, the site is now gone so it's back over to archive.org:
It's different, but somehow the same. Clicking through to the claim form, it seems the only way you can enter is if you agree to receive comms from all sorts of other parties:
Ok, one more, this time free-ukstuff.com which is also now a dead site, and not even indexed by archive.org. Next then, is findyourdegreenow.com which is - you're not gonna believe this - a dead site! Here's what it used to look like:
And again, it feels the same. Same same, but different.
To try and get a sense of how localised this data was, I queried out all the values in the "state" column. Is this a US-only data set? If that column is anything to go by, yes:
| FL 6437401 | |
| NY 4993674 | |
| PA 3739490 | |
| OH 3682141 | |
| MI 3116317 | |
| IL 3090785 | |
| NC 2983682 | |
| GA 2948814 | |
| NJ 2491437 | |
| VA 2108951 | |
| TN 1908740 | |
| MA 1851699 | |
| IN 1745983 | |
| MD 1690860 | |
| WI 1514865 | |
| AL 1480549 | |
| SC 1419050 | |
| MN 1345208 | |
| KY 1177492 | |
| CT 1119214 | |
| IA 834467 | |
| MS 813945 | |
| WV 434235 | |
| NH 371007 | |
| ME 348067 | |
| RI 323712 | |
| DE 311583 | |
| MT 239079 | |
| SD 195377 | |
| DC 156791 | |
| ND 153180 | |
| VT 135487 | |
| AE 311 | |
| PR 157 | |
| VI 13 |
Something didn't add up when I first saw that and after a quick check of the population of each US state, it become immediately obvious: there's no California, the most populous state in the country. Nor Texas, the second most populous state. In fact, with only 35 rows there's a bunch of US states missing. Why? Who knows, the only thing I can say for sure is that this is a subset of the population with some glaring geographical omissions.
Then there's another curveball - what about the URL quickquid.co.uk, that doesn't look very US-centric. Heading over there redirects to casheuronetukadministration.grantthornton.co.uk which advises that as of last month, "The Administration of CashEuroNet UK, LLC has closed and the Joint Administrators have ceased to act". So something has obviously been wound up, wonder what was there originally? I had to go back a few years to find this:
To my mind, this is more of the same ilk in terms of a service targeted at people after quick money. But it's clearly all in GBP and with a .co.uk TLD, this being right after I've just said all the states are in the US, what gives? Back to the source data, filter out the records based on that URL and sure enough, everyone has a US address. Grabbing a random selection of IP addresses had them all resolving to the US too so I have absolutely no idea how his geographically inconsistent set of data came to being.
And that's really the theme across the data set when doing independent analysis - how is this so? What service or process could have pulled the data together in this way? Maybe the people who this data actually refers to will have the answers, let's go and ask them.
Responses From Impacted HIBP Subscribers
We're approaching 4.5M subscribers to HIBP's free notification service now which makes for a great corpus of people I can reach out to when doing breach verification. I grabbed a handful of addresses from this data set and asked them if they could help out. I sent those that responded positively their full record and asked some questions about the legitimacy of the data, and where they thought it might have come from, here's what they said:
1. The data is mostly accurate.
A few things are off, such as date of birth (could very well be a fake one I've entered before) and details of household members.
There are a lot of columns with single-letter values, which I can't verify without knowing what they mean.
But overall, it's quite accurate.
2. No idea where it came from, sorry. There is a URL in the third-to-last column, but it doesn't seem like a website I would have used before.
I looked through the csv file and couldn't find anything I recognized. I saw the names [redacted], [redacted] and [redacted]- I don't know anyone by those names. I live in Ontario, Canada, but addresses in the file were located in the united states.
Data says I have one child between the ages of 0 and 2, but that's not true - my only son is five. Birth date is wrong - my birthday is [redacted], but the file says [redacted].
There were a few urls in the file and I don't recognize any of them.
Not sure if this last thing is relevant or not. I sometimes get emails intended for other people. I searched my inboxes for the names [redacted] and [redacted]. Nothing came up for [redacted], but I do see an email for [redacted] from [redacted]. I searched through the csv to see if anything matched the data in the email (member number, confirmation number), but nothing matched.
I also noticed that although my email address ([redacted]) is in the csv data, there's also another email address ([redacted]) which is not mine.
I'm not sure if that's helpful or not, but if there's anything more I can do, let me know. :)
As far as name and address they are correct. number of ppl living at the house has changed. The other information I can't seem to understand what the information for example under column AQ row 2 it has a U and I don't know what the U is for. I have noticed that some information is really outdated, so I wouldn't know where the data originated from.
Thank you for sharing, I took a look at the data, let me see if I can answer your questions:
1. While that is my email, the rest of the data actually belongs to an immediate family member. With the exception of a few outdated fields, the data on my family member is correct.
2. I am unfamiliar with Acxiom and am unsure of where this data originated from. I want to note that I have recently been doxxed and have reason to believe data breaches may have been used; however, the data you've provided here was not used in the attacks, to my knowledge.
Please let me know if you have any other questions, or if there is anything else I may do to help.
"Mostly accurate". The feeling I have when reading this is that whoever is responsible for this corpus of data has put it together from multiple sources and quite likely made some assumptions along the way. I can picture how that would happen; imagine trying to match various sources of data based on human-provided text fields in order to "enrich" the collection.
Analysis by Acxiom
This isn't the fist time Acxiom has had to deal with misattribution, and they'd seen exactly the same data set passed around before. Think about it from their perspective: every time there's a claim like this they need to treat it as though it could be legitimate, because we've all seen what happens when an organisation brushes off a disclosure attempt (I could literally write a book about this!) Thus it becomes a burdensome process for them as they repeat the same analysis over and over again, each time drawing the same conclusion.
And what was that conclusion? Simply put, the circulating data didn't align with their own. They're in the best position of all of us to draw that conclusion as they have access to both data sets and whilst I suspect some people may retort with "how do you know you can trust them", not only do I not have a good reason to doubt their findings, I also don't have a good reason to attribute it to them. Every reference I've seen to Acxiom has been from whoever is handing the data around; I've been able to find absolutely nothing within the data set itself to tie it back to them. In almost all breaches I've processed, the truth is in the data and there's nothing here that points the finger at them.
I offered Acxiom the opportunity to further clarify their position with a statement which I've included in its entirety here:
“Acxiom has worked to build a reputation over the course of fifty years for having the highest standards around data privacy, data protection and security. In the past, questionable organizations have falsely attached our name to a data file in an attempt to create a deceitful sense of legitimacy for an asset. In every instance, Acxiom conducts an extensive analysis under our cyber incident response and privacy programs. These programs are guided by stakeholders including working with the appropriate authorities to inform them of these crimes. The forensic review of the case that Troy has looked into, along with our continuous monitoring of security, means we can conclusively attest that the claims are indeed false and that the data, which has been readily available across multiple environments, does not come from Acxiom and is in no way the subject of an Acxiom breach.
Acxiom’s Commitment To Data Protection/ Data Privacy:
We value consumer privacy. U.S. consumers who would like to know what information Acxiom has collected about them and either delete it or opt out of Acxiom’s marketing products, may visit acxiom.com/privacy for more information.”
Summary
The email addresses from the data set have now been loaded into HIBP and are searchable. One point of note that became evident after loading the data is that 94% of the email addresses has already been pwned. That's a very high number (a quick look through the HIBP Twitter feed shows the count is normally between 40% and 80%), and it suggests that this corpus of data may be at least partially constructed from other data already in circulation.
Because the question will inevitably come up, no, I won't send you your full record, I simply don't have the capacity to operate as a personal data lookup and delivery service. I know it's frustrating finding yourself in a breach like this and not being able to take any action, all you can really do at this point is treat it as another reminder of how our data spread around the web and often, we have no idea about it.
Full disclosure: I have absolutely no commercial interest in Acxiom, no money has changed hands and I wasn't incentivised in any way, I just want everyone to have a much healthier suspicion when alleging the source of a data breach 🙂
https://www.troyhunt.com/data-breach-misattribution-acxiom-live-ramp/
Published: 2022 11 22 20:06:51
Received: 2023 02 09 08:40:37
Feed: Troy Hunt's Blog
Source: Troy Hunt's Blog
Category: Cyber Security
Topic: Cyber Security
Views: 26
