Welcome to our
Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.Common Attacks Against Modems
published on 2014-12-14 19:40:00 UTC by UnknownContent:
0x01: Introduction to Modems
The term DSL modem is technically used to describe "a modem which connects to a single computer, through a USB port or is installed in a computer PCI slot". The more common DSL router which combines the function of a DSL modem and a home router is a standalone device which could be connected to multiple computers through multiple Ethernet ports or an integral wireless access point. Also called as a "residential gateway", a DSL router usually manages the connection and sharing of the DSL service in a home or small office network.
Most consumer DSL lines use one of several variations and varieties of Asymmetric DSL (ADSL). The "asymmetric" DSL here means that more of the bandwidth of the line is dedicated to downstream (download) data than upstream (upload) data. Hence, download rates are faster than upload rates since most users download much larger quantities of data than they actually upload. Because the telephone lines were never designed to carry such high frequency signals, DSL is distance-sensitive. The farther away from the switching center the modem is, the longer the telephone wires, the weaker the signal, and the lower the data rate that the modem can achieve. Users in metropolitan areas, close to switching centers, may have access to higher rate service, up to 8 Mbit/s than the expected rate for the same service in remote areas.
Reference: en.wikipedia.org/wiki/DSL_modem
Most consumer DSL lines use one of several variations and varieties of Asymmetric DSL (ADSL). The "asymmetric" DSL here means that more of the bandwidth of the line is dedicated to downstream (download) data than upstream (upload) data. Hence, download rates are faster than upload rates since most users download much larger quantities of data than they actually upload. Because the telephone lines were never designed to carry such high frequency signals, DSL is distance-sensitive. The farther away from the switching center the modem is, the longer the telephone wires, the weaker the signal, and the lower the data rate that the modem can achieve. Users in metropolitan areas, close to switching centers, may have access to higher rate service, up to 8 Mbit/s than the expected rate for the same service in remote areas.
Reference: en.wikipedia.org/wiki/DSL_modem
0x02: Market Share
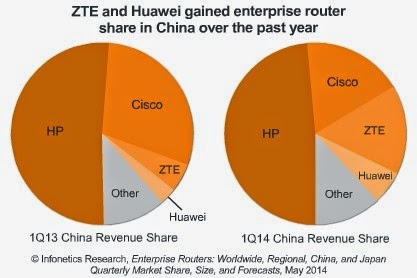
The modem manufacturers mostly are mostly chinese based . Research shows that companies like ZTE & Huawei are doing very well and have gained enterprise router share in china over the past year. In China ZTE is placed third player in 2013 and 2014 with dizzying rise this year than the popular consortium Cisco. (Which happens to be more secure). This is also due to the fact that cisco's products are very costly and difficult for the home users to afford.
0x03: Backups& Backdoors
All modems include Backup files mainly because of the need to recover the modem to the original state after a reset. However, knowing the direct link to the backup file puts the modem directly in danger. All an attacker has to do is request the backup file and view it; mostly this is juicy plain info that contains passwords, ISP configurations.
Knowing this however, some vendors try to encrypt the contents that are inside these files. So downloading this would be useless for the attacker. But this isn’t entirely impossible as lots of vendors tend to use weak encryption mechanisms to encrypt backup file. And research done by white hats such as Osanda Malith shows that. He for example provided a PoC tool used to decrypt these rom-0 (Backup) files from most modems, including ZTE and TP-Link.
Knowing this however, some vendors try to encrypt the contents that are inside these files. So downloading this would be useless for the attacker. But this isn’t entirely impossible as lots of vendors tend to use weak encryption mechanisms to encrypt backup file. And research done by white hats such as Osanda Malith shows that. He for example provided a PoC tool used to decrypt these rom-0 (Backup) files from most modems, including ZTE and TP-Link.
Most of the chinese Vendors such as ZTE are banned from the US, one because they being incredibly insecure and two because, they put malicious backdoors to snoop and eavesdrop on individuals and organizations.
Lots of trusted companies such as TP-Link, Huawei and other chinese companies have a record of placing backdoors in their products. These backdoors are normally in form of open ports which on connecting would provide a reverse shell. The ports are often found to be high in number to make it harder to detect.
One of such examples can be found here. This lets them capture sensitive files and sometimes sell it for residing countries. This strategy is great one for governments to spy on their citizens as well as for great as a part of a cyber attack against a particular country. So for example: A country could sell cheap backdoored modems to a target country, and in case the modems end up being used on military and sensitive systems, then they have hit a jackpot.
0x04: Default Configuration details and Hardcoded Credentials
Apparently, all if not most modems come with very easy to guess password configurations. Infact, most of them are identical like: username:admin and password: admin. Most people do not change the configuration details and most ISP’s leave this as default.
This amazingly is a good news for malicious users. Because all they have to do is know the vendor and they can get their hands on it easily using sites such as http://www.routerpasswords.com/ to extract information.
This amazingly is a good news for malicious users. Because all they have to do is know the vendor and they can get their hands on it easily using sites such as http://www.routerpasswords.com/ to extract information.
0x05: XSRF and XSS
These two are two of the most common flaws in the history of
web security. Mmost ZTE modems do not use anti-XSRF tokens (Used to prevent CSRF Attacks) on any sensitive request.
XSS is even more worsed because if one found an XSS flaw in any modem (which
is likely), he can send that link to a logged in administrator and perform any
action in behalf of the admin, this could be done by stealing the XSRF-Token. Also, an XSS could also allow session hijacking and other browser attacks.
XSRF flaws are more commonly found in modems as opposed to xss due to the fact that
modems use HTTP authentications most of the time. So Headers are mainly used in communications
protocols to communicate with one another. This makes it harder for the modem to
detect and create anti-csrf tokens other than to compare it.
Because of these or just because of careless developing it
is sometimes possible in to tricking admins changing passwords, issuing
commands or easing access.
0x06: Social Engineering
What would you say if a blocked number called you and told you that she is from your ISP and she needs your credentials in order to add/maintain the new and revised 3G technology into your modem. Or even she asks you to maintain security flaws in your modem? You surly never expect this to be a troll. I mean, why would you? And then next thing you know, she snooped your configuration password. Knowing this password could mean (since lots of people use same passwords) that she got access to email password, financial account, etc.
0x07: Exploit Databases
Many Exploit databases hold juicy info about modems. Including default configurations, XSRF/XSS/LFI flaws, logical issues, backdoors. So all you need to do is to find the modem version and give a search on exploit databases such as exploit-db.com, 1337day.com etc
So say, in case you found an exploit against a previous version of a modem, however not for the exact version. This necessary doesn't mean yours isn’t vulnerable to the particular exploit you found. Infact most vendors use same architecture to construct the web architecture of their modems. So one XSS on one model could mean XSS on all other vendor modems.
So say, in case you found an exploit against a previous version of a modem, however not for the exact version. This necessary doesn't mean yours isn’t vulnerable to the particular exploit you found. Infact most vendors use same architecture to construct the web architecture of their modems. So one XSS on one model could mean XSS on all other vendor modems.
0x08: Eavesdropping
The lack of SSL usually means bad luck for modems. Especially if it’s for office/public usage because the admin is always in risk of accessing any file from the modem. The reason being, that it is very easy to sniff ongoing traffic with with tools like Wireshark.
The fact that modems use login protocols like HTTP authentication puts them in more danger because when requesting any file, the modem should request the authentication header and the admin responds in (mostly Base64 form), and an attack easily can sniff this and decode the communication easily it.
Even when using SSL (note very few modems use it), it can still be insecure and even pose more risk. Recently, A lot of attacks have been identified against SSL protocols Heartbleed, POODLE to name a few.
The fact that modems use login protocols like HTTP authentication puts them in more danger because when requesting any file, the modem should request the authentication header and the admin responds in (mostly Base64 form), and an attack easily can sniff this and decode the communication easily it.
Even when using SSL (note very few modems use it), it can still be insecure and even pose more risk. Recently, A lot of attacks have been identified against SSL protocols Heartbleed, POODLE to name a few.
0x09: Denial Of Service
Denial of Service is one of the most annoying things I can think of next to a Log out CSRF. People with bad intentions can use this type of attack to knock a modem out of delivering internet and sometimes even let the modem reset itself.
This is really crazy for people trying to do their job. The fact this attack can easily be turned an untraceable attack can make your business day a big pain just because you choose to use a vulnerable modem.
Most modems by design don’t hold more HDD than 25MB and less than 2MB ram with no DOS protections. This usually means they can handle limited amount of data with huge amount of time. All an attacker has to do is send more requests than the modem can handle and hence exhausting it's memory and resulting in a DOS.
0x10: Lack Of Updates
Modem users seldom receive updates for modems in case a critical vulnerabilities have been identified in the wild, and a lot of them don't really have a mechanism for providing OTA (Over the Air) updates. A lot of times, users manually have to upgrade the firmware and ofcourse which is not possible for people having lack or no technical knowledge.
This is really crazy for people trying to do their job. The fact this attack can easily be turned an untraceable attack can make your business day a big pain just because you choose to use a vulnerable modem.
Most modems by design don’t hold more HDD than 25MB and less than 2MB ram with no DOS protections. This usually means they can handle limited amount of data with huge amount of time. All an attacker has to do is send more requests than the modem can handle and hence exhausting it's memory and resulting in a DOS.
0x10: Lack Of Updates
Modem users seldom receive updates for modems in case a critical vulnerabilities have been identified in the wild, and a lot of them don't really have a mechanism for providing OTA (Over the Air) updates. A lot of times, users manually have to upgrade the firmware and ofcourse which is not possible for people having lack or no technical knowledge.
0xA: Suggestions
- If you are an admin/user of a modem, Try not to stay logged in to make attacks like XSRF,XSS and ClickJacking less effective. .
- Try doing a little research about the modem model you are trying to buy. Google exploits for it, try to search if it uses secure connection (TLS), if it is vulnerable, why should you. Look for another.
- Try disabling remote access to decrease the attacker’s possibility of gaining access over the internet; since most of the modem exploits require LAN access, it’s a good thing to disable Telnet, web and even ftp access to modem remotely.
- Limit Physical Access. Because, most modems have a physical hard reset key/button, it should be noted most of them should remain in a secured environment where only authorized people can reach.
About the Author:
This
following article is a guest post by Paulos Yibelo. Yibelo is the
newest member of RHA family. He is a full time PHP coder and most of his
research is involved with application security. In his free time he
loves writing articles related to application security
http://paulosyibelo.blogspot.com/. - See more at:
http://www.rafayhackingarticles.net/2014/09/indepth-code-execution-in-php-part-two.html#sthash.b5OotKP6.dpuf
This following article is a guest post by Paulos Yibelo. Yibelo is the newest member of RHA family. He is a full time PHP coder and most of his research is involved with application security. In his free time he loves writing articles related to application security http://paulosyibelo.blogspot.com/
http://www.rafayhackingarticles.net/2014/12/common-attacks-against-modems.html
Published: 2014 12 14 19:40:00
Received: 2023 04 01 05:22:27
Feed: Ethical Hacking - Rafayhackingarticles
Source: Ethical Hacking - Rafayhackingarticles
Category: Cyber Security
Topic: Cyber Security
Views: 37