Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.[SANS ISC] Shadow IT Makes People More Vulnerable to Phishing
published on 2021-11-10 12:26:12 UTC by XavierContent:
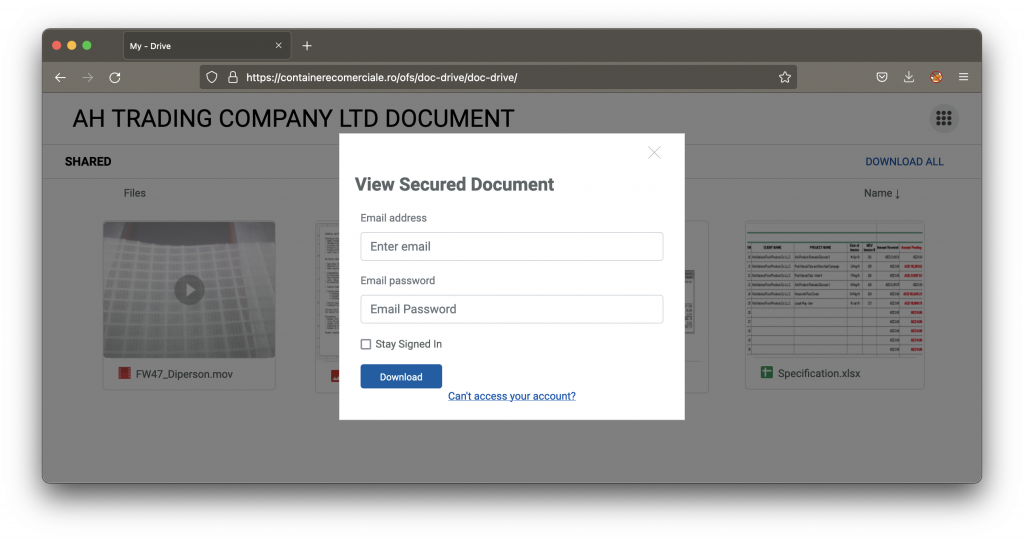
I published the following diary on isc.sans.edu: “Shadow IT Makes People More Vulnerable to Phishing“:
Shadow IT is a real problem in many organizations. Behind this term, we speak about pieces of hardware or software that are installed by users without the approval of the IT department. In many cases, shadow IT is used because internal IT teams are not able to provide tools in time. Think about a user who needs to safely exchange files with partners and no tool is available. A change request will be created to deploy one but, with the lack of (time|money|resources), the project will take time. Unfortunately, the user needs the tool now, so an alternative path will be used like a cloud file sharing service… [Read more]
The post [SANS ISC] Shadow IT Makes People More Vulnerable to Phishing appeared first on /dev/random.
https://blog.rootshell.be/2021/11/10/sans-isc-shadow-it-makes-people-more-vulnerable-to-phishing/
Published: 2021 11 10 12:26:12
Received: 2021 11 10 13:04:11
Feed: /dev/random
Source: /dev/random
Category: Cyber Security
Topic: Cyber Security
Views: 35
