Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.Using Fake Reviews to Find Dangerous Extensions
published on 2021-05-29 16:14:47 UTC by BrianKrebsContent:
Fake, positive reviews have infiltrated nearly every corner of life online these days, confusing consumers while offering an unwelcome advantage to fraudsters and sub-par products everywhere. Happily, identifying and tracking these fake reviewer accounts is often the easiest way to spot scams. Here’s the story of how bogus reviews on a counterfeit Microsoft Authenticator browser extension exposed dozens of other extensions that siphoned personal and financial data.
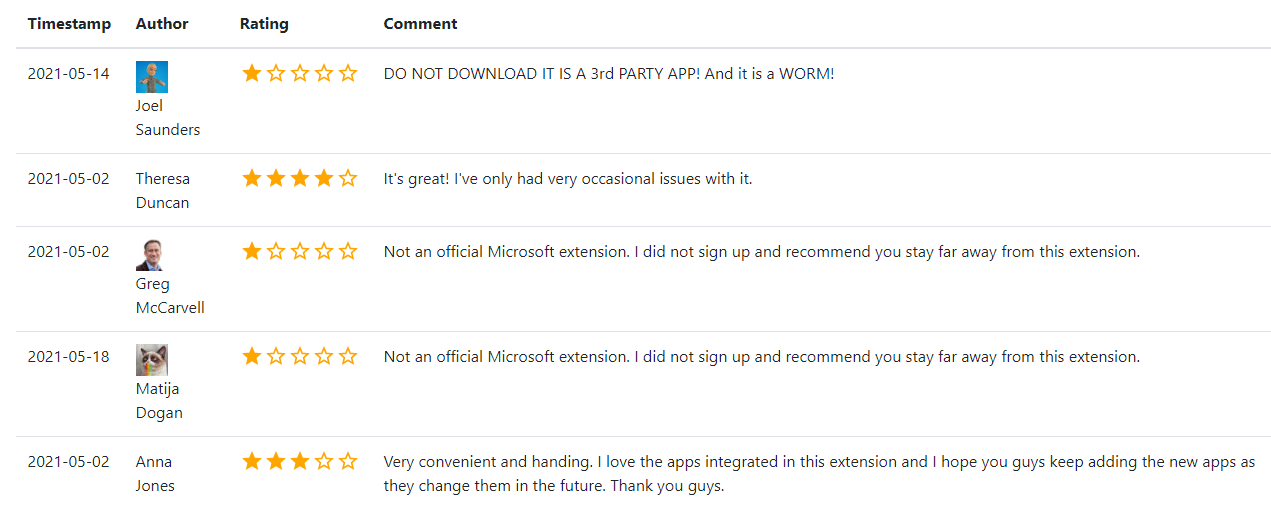
Comments on the fake Microsoft Authenticator browser extension show the reviews for these applications are either positive or very negative — basically calling it out as a scam. Image: chrome-stats.com.
After hearing from a reader about a phony Microsoft Authenticator extension that appeared on the Google Chrome Store, KrebsOnSecurity began looking at the profile of the account that created it. There were a total of five reviews on the extension before it was removed: Three Google users gave it one star, warning people to stay far away from it; but two of the reviewers awarded it between three and four stars.
“It’s great!,” the Google account Theresa Duncan enthused, improbably. “I’ve only had very occasional issues with it.”
“Very convenient and handing,” assessed Anna Jones, incomprehensibly.
Google’s Chrome Store said the email address tied to the account that published the knockoff Microsoft extension also was responsible for one called “iArtbook Digital Painting.” Before it was removed from the Chrome Store, iArtbook had garnered just 22 users and three reviews. As with the knockoff Microsoft extension, all three reviews were positive, and all were authored by accounts with first and last names, like Megan Vance, Olivia Knox, and Alison Graham.
Google’s Chrome Store doesn’t make it easy to search by reviewer. For that I turned to Hao Nguyen, the developer behind chrome-stats.com, which indexes and makes searchable a broad array of attributes about extensions available from Google.
Looking at the Google accounts that left positive reviews on both the now-defunct Microsoft Authenticator and iArtbook extensions, KrebsOnSecurity noticed that each left positive reviews on a handful of other extensions that have since been removed.
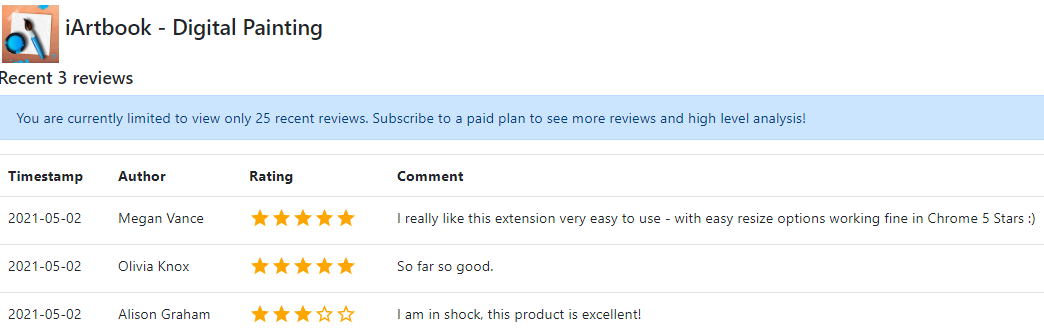
Reviews on the iArtbook extension were all from apparently fake Google accounts that each reviewed two other extensions, one of which was published by the same developer. This same pattern was observed across 45 now-defunct extensions.
Like an ever-expanding venn diagram, a review of the extensions commented on by each new fake reviewer found led to the discovery of even more phony reviewers and extensions. In total, roughly 24 hours worth of digging through chrome-stats.com unearthed more than 100 positive reviews on a network of patently fraudulent extensions.
Those reviews in turn lead to the relatively straightforward identification of:
-39 reviewers who were happy with extensions that spoofed major brands and requested financial data
-45 malicious extensions that collectively had close to 100,000 downloads
-25 developer accounts tied to multiple banned applications
The extensions spoofed a range of consumer brands, including Adobe, Amazon, Facebook, HBO, Microsoft, Roku and Verizon. Scouring the manifests for each of these other extensions in turn revealed that many of the same developers were tied to multiple apps being promoted by the same phony Google accounts.
Some of the fake extensions have only a handful of downloads, but most have hundreds or thousands. A fake Microsoft Teams extension attracted 16,200 downloads in the roughly two months it was available from the Google store. A counterfeit version of CapCut, a professional video editing software suite, claimed nearly 24,000 downloads over a similar time period.
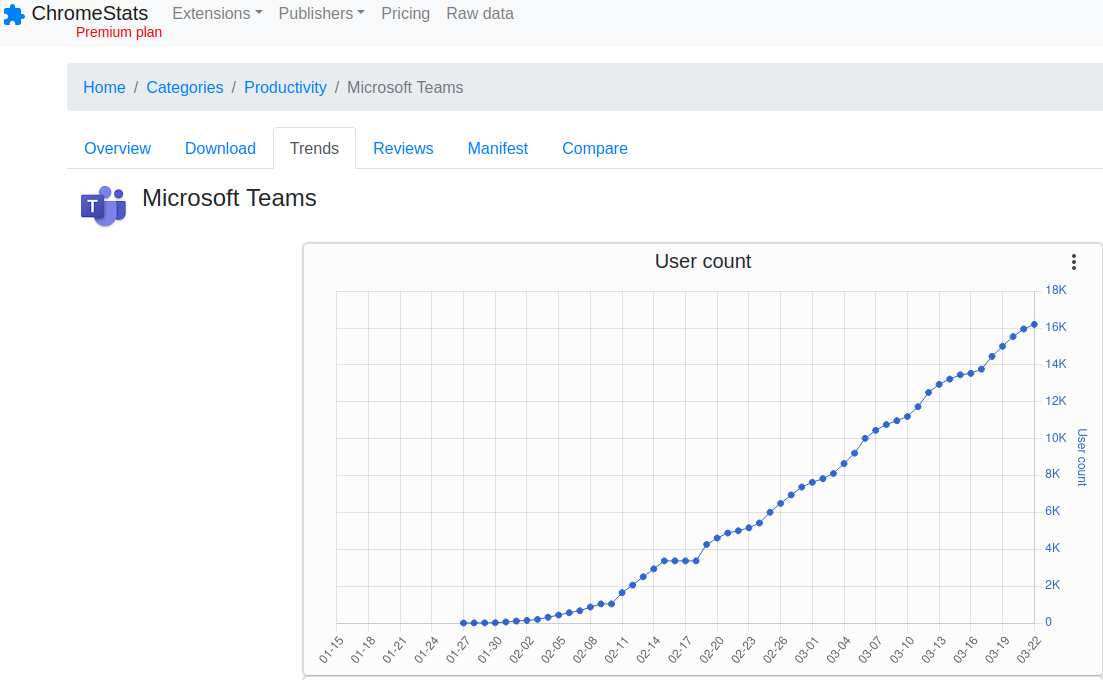
More than 16,000 people downloaded a fake Microsoft Teams browser extension over the roughly two months it was available for download from the Google Chrome store.
Unlike malicious browser extensions that can turn your PC into a botnet or harvest your cookies, none of the extensions examined here request any special permissions from users. Once installed, however, they invariably prompt the user to provide personal and financial data — all the while pretending to be associated with major brand names.
In some cases, the fake reviewers and phony extension developers used in this scheme share names, such as the case with “brook ice,” the Google account that positively reviewed the malicious Adobe and Microsoft Teams extensions. The email address brookice100@gmail.com was used to register the developer account responsible for producing two of the phony extensions examined in this review (PhotoMath and Dollify).
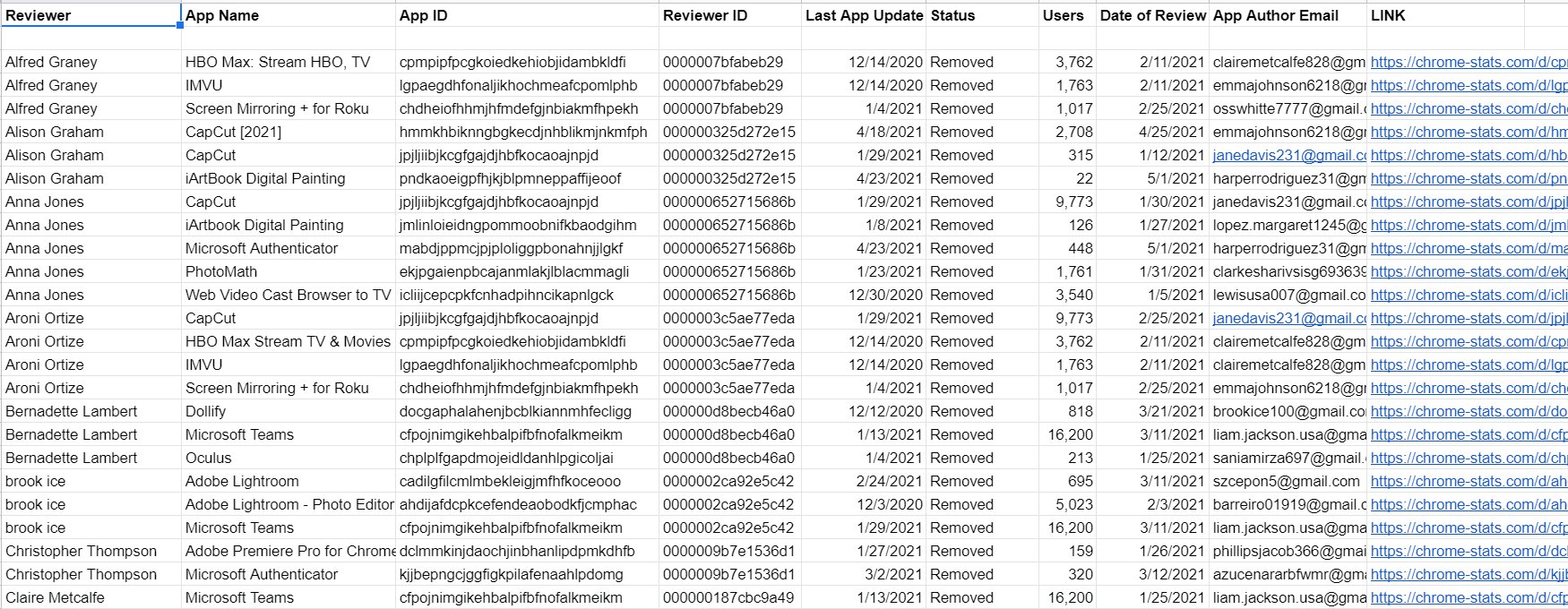
Some of the data that informed this report. The full spreadsheet is available as a link at the end of the story.
As we can see from the spreadsheet snippet above, many of the Google accounts that penned positive reviews on patently bogus extensions left comments on multiple apps on the same day.
Additionally, Google’s account recovery tools indicate many different developer email addresses tied to extensions reviewed here share the same recovery email — suggesting a relatively few number of anonymous users are controlling the entire scheme. When the spreadsheet data shown above is sorted by email address of the extension developer, the grouping of the reviews by date becomes even clearer.
KrebsOnSecurity shared these findings with Google and will update this story in the event they respond. Either way, Google somehow already detected all of these extensions as fraudulent and removed them from its store.
However, there may be a future post here about how long that bad extension identification and removal process has taken over time. Overall, most of these extensions were available for two to three months before being taken down.
As for the “so what?” here? I performed this research mainly because I could, and I thought it was interesting enough to share. Also, I got fascinated with the idea that finding fake applications might be as simple as identifying and following the likely fake reviewers. I’m positive there is more to this network of fraudulent extensions than is documented here.
As this story illustrates, it pays to be judicious about installing extensions. Leaving aside these extensions which are outright fraudulent, so many legitimate extensions get abandoned or sold each year to shady marketers that it’s wise to only trust extensions that are actively maintained (and perhaps have a critical mass of users that would make noise if anything untoward happened with the software).
According to chrome-stats.com, the majority of extensions — more than 100,000 of them — are effectively abandoned by their authors, or haven’t been updated in more than two years. In other words, there a great many developers who are likely to be open to someone else buying up their creation along with their user base.
The information that informed this report is searchable in this Google spreadsheet.
https://krebsonsecurity.com/2021/05/using-fake-reviews-to-find-dangerous-extensions/
Published: 2021 05 29 16:14:47
Received: 2021 06 06 09:04:53
Feed: Krebs on Security
Source: Krebs on Security
Category: Cyber Security
Topic: Cyber Security
Views: 19
